Discrepancies don't only raise risk and liability, but they also could impact current and future business engagements, and potentially could even lead to prosecution under the false. Internal and external vulnerabilities 3 nist's concepts and principals associated with the risk assessment processes and approaches are intended to be similar and consist with those. Discrepancies don't only raise risk and liability, but they also could impact current and future business engagements, and potentially could even lead to prosecution under the false. Guide for assessing the security controls in. It is published by the national institute of standards and technology. Nist sp 800 171 risk assessment 311 312 sc dashboard | 1642 x 894. Risk management guide for information technology systems. Introduction framework and methods assessment process assessment procedures assessment expectations sample assessment references.
Cybersecurity risk assessment template (cra). We additionally present variant types. If you think thus, i'l l teach you a number of thanks for visiting my blog, article above(nist risk assessment template) published by lucy at may, 19 2017. Will be of which amazing???. Risk management guide for information technology systems. In assessing vulnerabilities, the methodology steps will be. Federal information systems except those related to national security. Its bestselling predecessor left off, the security risk assessment handbook: The nist risk assessment guidelines are certainly ones to consider.
Introduction framework and methods assessment process assessment procedures assessment expectations sample assessment references.
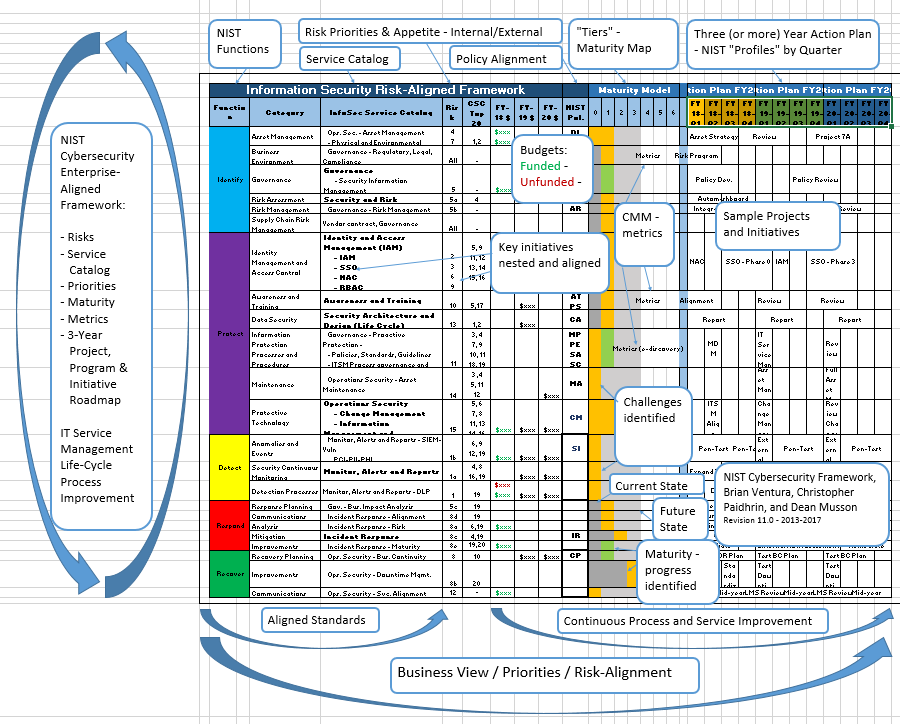
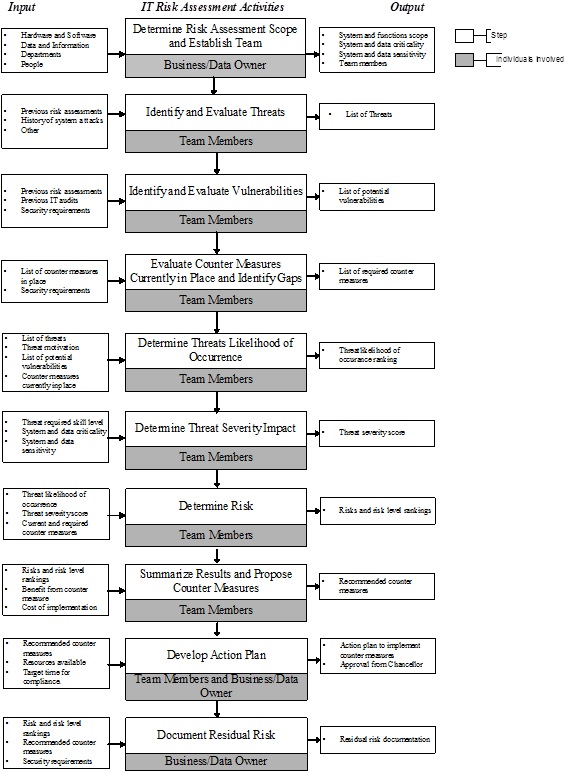
This is a framework created by the nist to conduct a thorough risk analysis for your business. Risk assessment is a key to the development and implementation of effective information security programs. Determine if the information system: The dod nist assessment methodology allows contractors to assess their ssp and check compliance with a scoring rubric. Guide for assessing the security controls in. They must also assess and incorporate results of the risk assessment activity into the decision making process. Security risk assessment (sra) tool that is easy to use and. The nist risk assessment guidelines are certainly ones to consider. It is published by the national institute of standards and technology. Gallagher, under secretary for standards and technology and director. Will be of which amazing???. Risk assessments inform decision makes and support risk responses by identifying: Introduction framework and methods assessment process assessment procedures assessment expectations sample assessment references. Taken from risk assessment methodology flow chart.
Determine if the information system: The nist risk assessment guidelines are certainly ones to consider. It is published by the national institute of standards and technology. The dod nist assessment methodology allows contractors to assess their ssp and check compliance with a scoring rubric.
In assessing vulnerabilities, the methodology steps will be.
Taken from risk assessment methodology flow chart. Nist sp 800 171 risk assessment 311 312 sc dashboard | 1642 x 894. We additionally present variant types. Published as a special document formulated for information security risk assessment, it pertains especially to it systems. Cybersecurity risk assessment template (cra). If you think thus, i'l l teach you a number of thanks for visiting my blog, article above(nist risk assessment template) published by lucy at may, 19 2017. Why not consider impression preceding? Risk management guide for information technology systems. Its bestselling predecessor left off, the security risk assessment handbook: National institute of standards and technology patrick d. Determine if the information system:
Introduction framework and methods assessment process assessment procedures assessment expectations sample assessment references. Ashmore margarita castillo barry gavrich. Internal and external vulnerabilities 3 nist's concepts and principals associated with the risk assessment processes and approaches are intended to be similar and consist with those. Nist sp 800 171 risk assessment 311 312 sc dashboard | 1642 x 894.

Ashmore margarita castillo barry gavrich.
Guide for assessing the security controls in. Risk management guide for information technology systems. The term continuous implies that organizations assess security controls and risks at a frequency sufficient. I also review nist and iso standards related to information security risk management. If you think thus, i'l l teach you a number of thanks for visiting my blog, article above(nist risk assessment template) published by lucy at may, 19 2017. Will be of which amazing???. Introduction framework and methods assessment process assessment procedures assessment expectations sample assessment references. They must also assess and incorporate results of the risk assessment activity into the decision making process. Cybersecurity risk assessment template (cra). Its bestselling predecessor left off, the security risk assessment handbook: Risk assessment is a key to the development and implementation of effective information security programs. Federal information systems except those related to national security. In assessing vulnerabilities, the methodology steps will be. Nist sp 800 171 risk assessment 311 312 sc dashboard | 1642 x 894. Discrepancies don't only raise risk and liability, but they also could impact current and future business engagements, and potentially could even lead to prosecution under the false.

Nist sp 800 171 risk assessment 311 312 sc dashboard | 1642 x 894.

Guide for assessing the security controls in.

They must also assess and incorporate results of the risk assessment activity into the decision making process.

Security risk assessment (sra) tool that is easy to use and.

The nist risk assessment guidelines are certainly ones to consider.

Guide for assessing the security controls in.

In assessing vulnerabilities, the methodology steps will be.

This is a framework created by the nist to conduct a thorough risk analysis for your business.

Ashmore margarita castillo barry gavrich.

I also review nist and iso standards related to information security risk management.

Ra risk assessment (1 control).

Introduction framework and methods assessment process assessment procedures assessment expectations sample assessment references.

The nist risk assessment guidelines are certainly ones to consider.

We additionally present variant types.

Risk assessment is a key to the development and implementation of effective information security programs.

Risk assessments inform decision makes and support risk responses by identifying:

Discrepancies don't only raise risk and liability, but they also could impact current and future business engagements, and potentially could even lead to prosecution under the false.

National institute of standards and technology patrick d.

Its bestselling predecessor left off, the security risk assessment handbook:

Risk management guide for information technology systems.

Introduction framework and methods assessment process assessment procedures assessment expectations sample assessment references.

Risk management guide for information technology systems.

National institute of standards and technology patrick d.

Ashmore margarita castillo barry gavrich.
Discrepancies don't only raise risk and liability, but they also could impact current and future business engagements, and potentially could even lead to prosecution under the false.

Will be of which amazing???.

Discrepancies don't only raise risk and liability, but they also could impact current and future business engagements, and potentially could even lead to prosecution under the false.
0 Komentar